Glossary: HR Data Security
Imagine this scenario. You have just found a violation in your payroll system. Employee bank details and home addresses are sensitive information that are now exposed to the dark web.
It is not a technical glitch. It is a reputational and legal nightmare. HR data security will no longer be an IT issue in the future.
It is fundamental to the business. It secures your brand and your people. Encryption, compliance, and access controls have now become a concern for HR teams.
This blog is your technical guide. We shall deconstruct the what, why, and how. You will get to know the most important terms and steps.
You will also see the support of modern platforms. Lanteria HR is one example. Let us explore workforce protection.
What Is HR Data Security?
HR data security is a set of technologies and protocols that safeguard the information of employees. This contains the bank details, addresses, and performance reviews. It also has files associated with hiring and offboarding.
It is built on the CIA Triad. It is that is Confidentiality, Integrity, and Availability. The data should only be accessed by authorized persons.
The data must stay accurate. It should also be there when you require it. All three are backed by strong controls.
The new security is more than passwords. It employs multi-layered system defenses. It safeguards information throughout the HR lifecycle.
Helpful Resource: What is Core HR?
Why Is Security Non-Negotiable For HR?

Global teams have high stakes. One violation will attract heavy penalties. It is also capable of generating lawsuits and audits.
Rules increase the stress. Negligence is punished by GDPR and CCPA. A single incident will cost millions.
Trust breaks even faster. Safety is the default expectation of employees. Trust is difficult to gain once lost.
The integrity of data is also important. Payroll fails in case a hacker alters bank details. That brings operational disorder.
Mistakes propagated through systems. Bad data has an impact on benefits and reporting. It is also able to destroy tax filings and compliance records.
This risk is mitigated by modern HRM solutions. They apply checks, logs, and controls. They also ensure quicker response to incidents.
Helpful Resource: Microsoft-Native HR Software Explained for 2026
Technical Categories Of HR Data Security
In order to create a robust defense, you should know the types of control. There is a risk in each category. They collectively constitute your foundation.
No single category is enough. The majority of breaches are multidirectional. Your controls should be in layers.
Key Technical Terms You Should Know
- Encryption at Rest: This secures the stored information on the drives or the cloud drives. It is possible to steal hardware, but files remain unreadable. It minimizes post-access damage
- Encryption In Transit: Here data is secured during transit. As an example, the reports issued by the HRIS to the device of a manager. It assists in avoiding interception.
- Multi-Factor Authentication (Mfa): It involves two or more identity verifications. It prevents the majority of takeovers of accounts. It is a high-impact control that is simple.
- Audit Trails: This is a chronological record of activity. They indicate the people who accessed information and when. They facilitate investigations and compliance evidence.
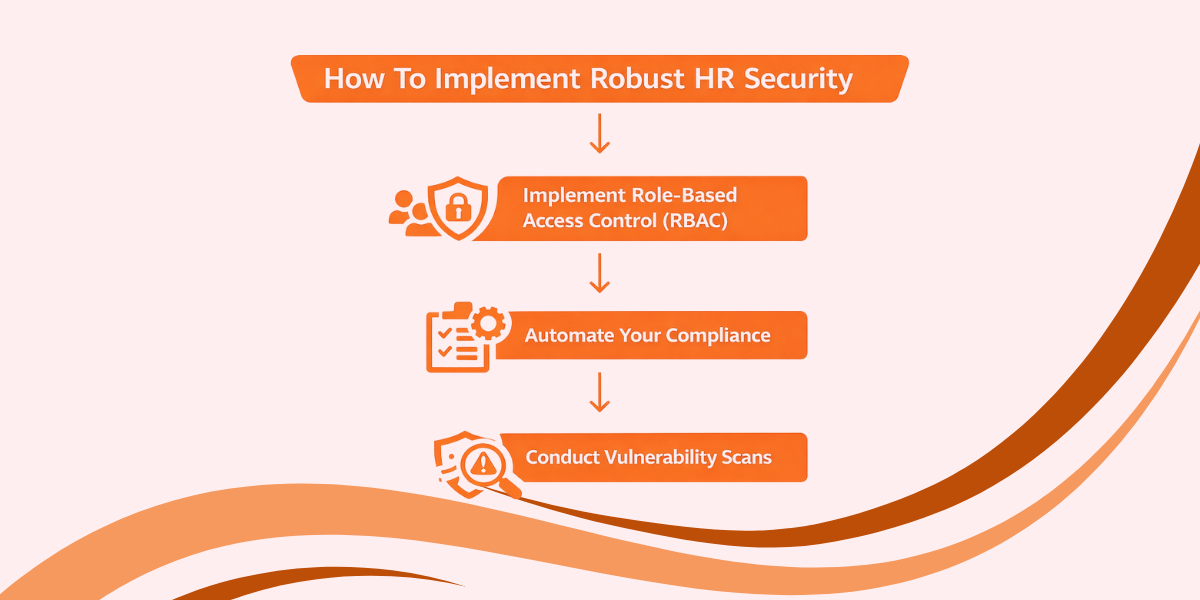
How To Implement Robust HR Security
Security is something you cannot set and forget. Threats change constantly. Your controls have to change as well.
Begin with secure storage and access. Microsoft SharePoint is used in the HR documents of many teams. It promotes enterprise-level security.
1. Implement Role-Based Access Control (Rbac)
Do not allow everybody complete access. Apply the Least Privilege Principle. One should not see more than what they need.
A recruiter can view resumes. They do not need salary data. RBAC simplifies this on the basis of roles.
Review access on a schedule. The roles in HR workflows change frequently. Take down access whenever individuals switch teams.
2. Automate Your Compliance
Paper-based monitoring leaves loopholes. Human beings do not take the right steps in an emergency. This risk is minimized by automation.
Select compliance workflow tools. Search alerts, logging, and policy enforcement. This is even more important in various nations.
Keep evidence ready. Audits do not usually want promises; they want evidence. You can respond quickly with the assistance of automated reporting.
3. Conduct Regular Vulnerability Scans
Imagine this to be ethical testing. You identify weak points first before the attackers. It helps you fix issues early.
Run scans on a routine cycle. In addition to scanning after a significant change in the system. New integrations have the potential to introduce new risks.
Validate your defenses. Firewalls and rules are becoming outdated. They are still tested to work by regular audits.
Helpful Resource: Future-Proof Your HR with Secure Lanteria Solutions
TL;DR
HR data security safeguards data regarding employees with technical controls. It helps to follow rules and trust in workers. Minimize risk by use of encryption, MFA, and RBAC.
Conclusion
Securing HR data is a journey. Cybercriminal activities continue to evolve. Your security must keep pace.
This vocabulary provided you with the fundamentals. Now you get to know about encryption and access controls. There are steps that you also need to take today.
Do not wait for a breach. Begin with compliance automation, roles, and audits. Select platforms with security as their priority.
FAQs
What Is The Difference Between Data Privacy And Data Security?
Data privacy involves the right to access data. Preventing unauthorized access is called data security. Privacy is policy, whereas security is implementation.
Is Cloud-Based HR Software Secure?
Yes, when the provider is of a good standard. Look for SOC 2 Type II or ISO 27001. In addition, verify encryption, multi-factor authentication, and auditing.
How Often Should We Update Our Security Policies?
Periodically review policies (once a year). Inform them of substantial regulatory changes. Incidents or system upgrades should also be updated.
Scheduling a demo to explore how Lanteria HR assists in securing employee information.




























